
𝙾𝚏𝚏𝚒𝚌𝚒𝚊𝚕 𝚠𝚎𝚋𝚜𝚒𝚝𝚎 – spiderfoot.net
𝚆𝚑𝚊𝚝 𝚒𝚜 𝙾𝚂𝙸𝙽𝚃 – OSINT stands for Open-Source Intelligence. It refers to the practice of collecting, analyzing, and disseminating information that is publicly available and legally obtainable. This can include information from social media, websites, news articles, government reports, and other sources. OSINT is often used by organizations and individuals to gather information for various purposes, such as investigative journalism, business intelligence, cybersecurity, and law enforcement.
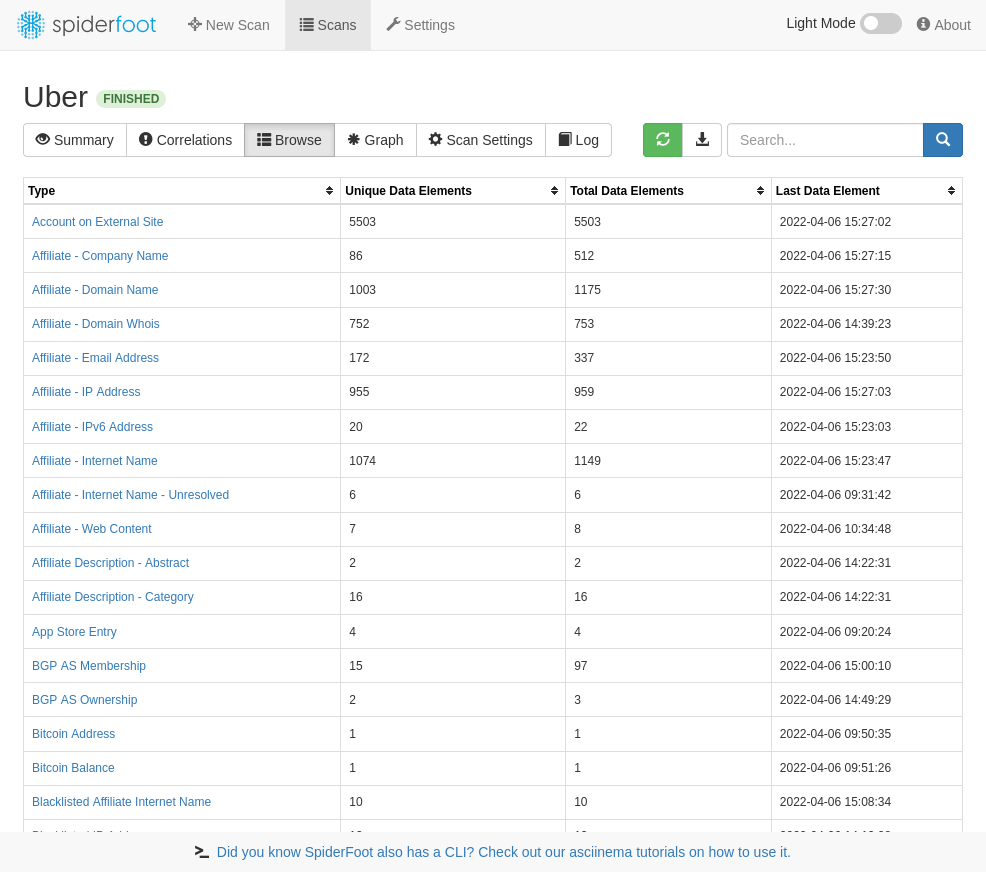
𝚆𝚑𝚊𝚝 𝚒𝚜 𝚂𝚙𝚒𝚍𝚎𝚛𝙵𝚘𝚘𝚝 🕷 – SpiderFoot is a tool that automates the process of gathering intelligence from various sources on the internet. It is designed to be used for OSINT (Open-Source Intelligence) purposes, and can be used to gather information on IP addresses, domains, email addresses, and other types of online identifiers. SpiderFoot can be used to gather information from a wide range of sources, including search engines, social media platforms, and public databases. It is commonly used by cybersecurity professionals, law enforcement agencies, and other organizations to gather information for various purposes, such as threat intelligence, incident response, and fraud detection.
FEATURES :-
- Web based UI or CLI
- Over 200 modules (see below)
- Python 3.7+
- YAML-configurable correlation engine with 37 pre-defined rules
- CSV/JSON/GEXF export
- API key export/import
- SQLite back-end for custom querying
- Highly configurable
- Fully documented
- Visualisations
- TOR integration for dark web searching
- Dockerfile for Docker-based deployments
- Can call other tools like DNSTwist, Whatweb, Nmap and CMSeeK
- Actively developed since 2012!
USES :-
SpiderFoot is a tool that automates the process of gathering intelligence about a given target on the internet. It is used to gather information from a wide range of sources, including search engines, Whois databases, DNS records, social media platforms, and other online resources. This information can be used to help organizations better understand their online presence and identify potential vulnerabilities, threats, and risks. SpiderFoot can be used by a variety of different organizations, including security professionals, investigators, and researchers.
You can target the following entities in a SpiderFoot scan:
- IP address
- Domain/sub-domain name
- Hostname
- Network subnet (CIDR)
- ASN
- E-mail address
- Phone number
- Username
- Person’s name
- Bitcoin address
SpiderFoot’s 200+ modules feed each other in a publisher/subscriber model to ensure maximum data extraction to do things like:
- Host/sub-domain/TLD enumeration/extraction
- Email address, phone number and human name extraction
- Bitcoin and Ethereum address extraction
- Check for susceptibility to sub-domain hijacking
- DNS zone transfers
- Threat intelligence and Blacklist queries
- API integration with SHODAN, HaveIBeenPwned, GreyNoise, AlienVault, SecurityTrails, etc.
- Social media account enumeration
S3/Azure/Digitalocean bucket enumeration/scraping - IP geo-location
- Web scraping, web content analysis
- Image, document and binary file meta data analysis
- Dark web searches
- Port scanning and banner grabbing
- Data breach searches.
Installing & running.
To install and run SpiderFoot, you need at least Python 3.7 and a number of Python libraries which you can install with pip. We recommend you install a packaged release since master will often have bleeding edge features and modules that aren’t fully tested
Stable build (packaged release) :-
- wget https://github.com/smicallef/spiderfoot/archive/v4.0.tar.gz
tar zxvf v4.0.tar.gz
- cd spiderfoot-4.0
- pip3 install -r requirements.txt
- python3 ./sf.py -l 127.0.0.1:5001
Cloning git master branch:-
- git clone https://github.com/smicallef/spiderfoot.git
- cd spiderfoot
- pip3 install -r requirements.txt
- python3 ./sf.py -l 127.0.0.1:5001
WRITING CORRELATION RULES :-
We have a comprehensive write-up and reference of the correlation rule-set introduced in SpiderFoot 4.0 here.
Also take a look at the template.yaml file for a walk through. The existing 37 rules are also quite readable and good as starting points for additional rules.
𝙵𝚘𝚛 𝚌𝚘𝚗𝚝𝚊𝚌𝚝📞